Download Malwarebytes for Mac (the free version) and you get a 14-day trial of the premium version with automatic (real-time) virus and malware protection. After 14 days, your trial reverts to a limited disinfection scanner. Buy the premium version now to prevent infection in the first place. Adware is unwanted software designed to throw advertisements up on your screen, most often within a web browser. Some security professionals view it as the forerunner of the modern-day PUP (potentially unwanted program). Mac malware is rare, but it does exist. If you thinking that your Mac has a virus and want advice about Mac malware removal you've come to the right place. Here's how to get a free virus scan to.
I seem to have gotten some type of adware/malware on my MacBook Pro running Catalina. Every few minutes, random tabs will open up with what seems like gibberish URLs, or sometimes advertisements to clothing sites. This seems to be happening even when the computer is in sleep mode, so these tabs p. Remove ExecutiveOperation adware from Safari. Uninstall suspicious Safari extensions. Open Safari and click on Safari button in the top left corner. Select Preferences in the menu that appears on the screen.
If Mac users are experiencing issues on their internet application like for example, it keeps on showing aggressive pop-up ads and redirects, there may be an adware that is commanding the browser to produce such objects. Aside from the annoyances from continuous ad display, adware is able to steal several information from the browser. It can track web user's data that are presently stored on the browser. Thus, Mac users' online privacy is already compromised. One adware that can perform such malicious tasks is called StandardBoost.
What is StandardBoost App?
Technically, StandardBoost was designed to perform as internet browser extension. But due to the usage of different intrusive tactics to penetrate the Mac computer, it was listed under the category of potentially unwanted application (PUA). Actually, StandardBoost is just another rendition of previously released malware like InputBalance, InitialMachine, and SimpleSearchGuide. All of these browser threats can contaminate the computer via different misleading online schemes.
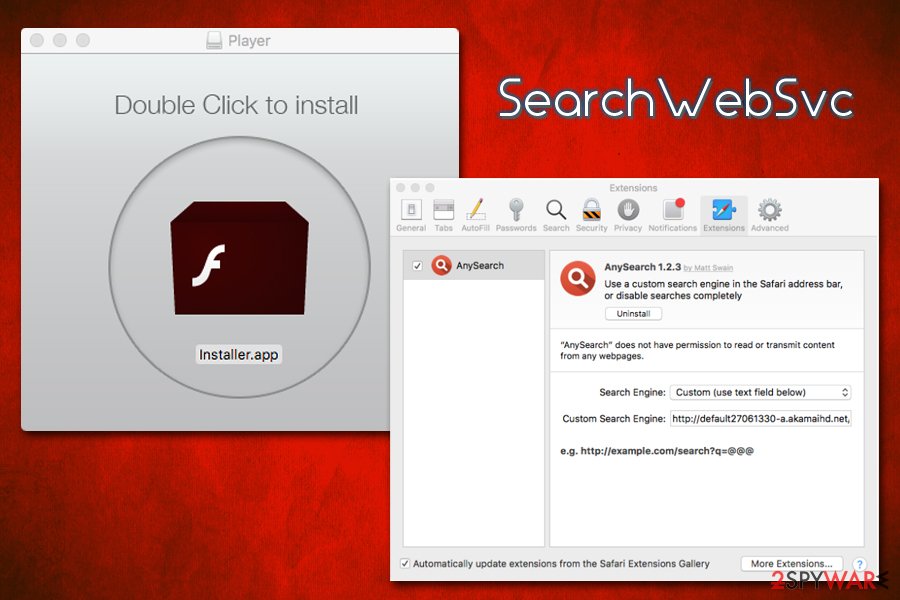
Attackers are employing techniques such as software bundling hoax, bogus software update, and malicious ad campaign that promotes StandardBoost as valuable browser extension. Of all these mentioned techniques, only the latter is requiring Mac user's intervention to install the app. The rests are relying on the hosts software to carry the adware inside the computer and run a simultaneous installation.
Risks of installing StandardBoost App
Ads that will show up on the browser during the existence of StandardBoost are unusual. In fact, they are not user-friendly. Most ads emerging from the adware infection are unsafe and could contain malicious links that forwards the browser pages to other questionable websites particularly ones that are offering fake software updates as shown in the image below.
The data tracking abilities of StandardBoost app could yield to identity theft. It is able to extract browsing and personal information such as favorite websites, browsing history, visited pages, username, password, and IP address or geographical location of Mac user. This information monitoring method by StandardBoost will persist as long as the unwanted browser extension is operational. In addition, the affected internet browser program will display an alert message 'StandardBoostd will damage your computer.'
Obviously, StandardBoost is a threat to online privacy and security of Mac users. Thus, immediate computer cleanup is recommended. Please follow the guide below to completely remove StandardBoost from the compromised computer and internet program. As stated, scan the computer with effective virus and malware removal tools to delete hidden malicious items associated with the threat.
Procedures to Remove StandardBoost from Mac
This area contains comprehensive procedures to help you remove adware and potentially unwanted program from the computer.
Guide on this page are written in a manner that can be easily understand and execute by Mac users.
Quick Fix - Scan the System with Combo Cleaner
Combo Cleaner is a trusted Mac utility application with complete antivirus and optimization features. It is useful in dealing with adware, malware, and PUP's. Moreover, it can get rid of adware like StandardBoost. You may need to purchase full version if you require to maximize its premium features.
1. Download the tool from the following page:
2. Double-click the downloaded file and proceed with the installation.
3. In the opened window, drag and drop the Combo Cleaner icon onto your Applications folder icon.
4. Open your Launchpad and click on the Combo Cleaner icon.
5. Wait until antivirus downloads its latest virus definition updates and click on 'Start Combo Scan' to start removing StandardBoost.
6. Free features of Combo Cleaner include Disk Cleaner, Big Files finder, Duplicate files finder, and Uninstaller. To use antivirus and privacy scanner, users have to upgrade to a premium version.
Proceed with the rest of the removal steps if you are comfortable in manually removing malicious objects associated with the threat.
Step 1 : Delete StandardBoost from Mac Applications
1. Go to Finder.
2. On the menu, click Go and then, select Applications from the list to open Applications Folder.
3. Find StandardBoost or any unwanted program.
4. Drag StandardBoost to Trash Bin to delete the application from Mac.
5. Right-click on Trash icon and click on Empty Trash.
Step 2 : Remove Browser Extensions that belongs to StandardBoost
1. Locate the add-on or extension that is relevant to the adware. To do this, please follow the following depending on affected browser.
Safari - Choose Preferences from the Safari menu, then click the Extensions icon. This will open a window showing all installed extensions.
Chrome - Select Preferences from the Chrome menu, and then click the Extensions link found on the left pane.
Firefox - Choose Add-ons from the Menu. Look at both the Extensions and Plug-ins lists when it opens a new window.
2. Once you have located StandardBoost, click on Remove or Uninstall, to get rid of it.
3. Close the browser and proceed to the next steps.
Step 3 : Delete Malicious Files that have installed StandardBoost
1. Select and copy the string below to your Clipboard by pressing Command + C on your keyboard.
~/Library/LaunchAgents
2. Go to your Finder. From the menu bar please select Go > Go to Folder..
3. Press Command + V on your keyboard to paste the copied string. Press Return to go to the said folder.
4. You will now see a folder named LaunchAgents. Take note of the following files inside the folder:
- com.StandardBoost
- unknown.download.plist
- unknown.ltvbit.plist
- unknown.update.plist
The term unknown is just a representation of the actual malware name. Attackers may masks the actual name with following:
- Standard Boost, InputBalance
If you cannot find the specified file, please look for any unfamiliar or suspicious entries. It may be the one causing StandardBoost to be present on your Mac. Arranging all items to see the most latest ones may also help you identify recently installed unfamiliar files. Please press Option + Command + 4 on your keyboard to arrange the application list in chronological order.
Important: Take note of all the suspicious files as you may also delete the same item on another folder as we go on.
5. Drag all suspicious files that you may find to Trash.
6. Please restart the computer.
7. Open another folder using the same method as above. Copy and Paste the following string to easily locate the folder.
~/Library/Application Support
8. Look for any suspicious items that are similar to the ones in Step 4. Drag them to the Trash.
9. Repeat the process on the following non-hidden folders (without ~):
/Library/LaunchAgents
/Library/LaunchDaemons
/Library/Application Support
10. Lastly, go to your Finder and open the Applications Folder. Look for subfolders with the following names and drag them to Trash.
Firefly stronghold crusader. - Standard Boost, InputBalance
Optional : For locked files that cannot be removed, do the following:
1. Go to Launchpad, Utilities folder, open Activity Monitor.

1. Go to Launchpad, Utilities folder, open Activity Monitor.
2. Select the process you want to quit.
3. Click on Force Quit button.
4. You may now delete or remove locked files that belongs to StandardBoost adware.
Step 4 : Double-check with MBAM Tool for Mac
1. Download Malwarebytes Anti-malware for Mac from this link:
2. Run Malwarebytes Anti-malware for Mac. It will check for updates and download if most recent version is available. This is necessary in finding recent malware threats including StandardBoost.
3. If it prompts to close all running web browser, please do so. Thus, we advise you to PRINT this guide for your reference before going offline.
4. Once it opens the user interface, please click on Scan button to start scanning your Mac computer.
5. After the scan, Malwarebytes Anti-malware for Mac will display a list of identified threats, StandardBoost is surely part of it. Be sure to select all items in the list. Then, click Remove button to clean the computer.
Step 5 : Remove StandardBoost from Homepage and Search
Safari
- Open your Safari browser.
- Go to Safari Menu located on upper left hand corner, and then select Preferences.
- Under General tab, navigate to Default Search Engine section and select Google or any valid search engine.
- Next, be sure that 'New Windows Open With' field is set to Homepage.
- Lastly, remove StandardBoost from the Homepage field. Replace it with your preferred URL to be set as your default homepage.
Google Chrome
- Open Chrome browser.
- Type the following on the address bar and press Enter on keyboard : chrome://settings/
- Look for 'On Startup' area.
- Select 'Open a specific page or set of pages'.
- Click on More Actions and select Edit.
- Enter the desired web address as your home page, replacing StandardBoost. Click Save.
- To set default search engine, go to Search Engine area.
- Click on 'Manage search engines..' button.
- Go to questionable Search Engine. Click on More Actions and Click 'Remove from list'.
- Go back to Search Engine area and choose valid entry from Search engine used in the address bar.
Mozilla Firefox
- Run Mozilla Firefox browser.
- Type the following on the address bar and hit Enter on keyboard : about:preferences
- On Startup area, select 'Show your home page' under 'When Firefox starts' field.
- Under Home Page field, type the desired URL to replace StandardBoost settings.
- To configure default search engine, select Search on left sidebar to display settings.
- Under Default Search Engine list, please select one.
- On the same page, you have an option to Remove unwanted search engine.
Optional : If unable to change browser settings, execute these steps:
Some user complains that there is no way to change browser settings because it is grayed out by StandardBoost. In such situation, it is important to check if there is unwanted profile. Please do the following:
1. Quit any running applications and launch System Preferences from your Dock.
2. Under System Preferences, click Profiles.
3. Select StandardBoost or any relevant profile from the left pane. See image below.
4. At the bottom of this window, click minus [-] button to delete the account. Please refer to image above.
5. Close the Profiles window and open the affected browser to change all settings associated with StandardBoost.
How to remove Safari Redirect Virus browser hijacker from Mac?
What is Safari Redirect Virus?
Rogue applications that are categorized as browser hijackers and modify Safari browser settings have a generic name: 'Safari Redirect Virus'. When installed, browser-hijacking apps change settings of the affected browser and record various information (usually browsing-related). Typically, people install these apps inadvertently.
Browser hijackers are categorized as potentially unwanted applications (PUAs). When installed, they modify browser settings such as default search engine, homepage, and new tab URL. They assign a specific URL to these settings, overwriting any previous values. Once these changes are made, users are redirected to the new URL or to visit a particular website when a browser window or new tab is opened, or a search query is entered into the URL bar. As the name suggests ('Safari Redirect Virus'), these browser hijackers target Safari browsers, however, PUAs of this type also target other popular browsers such as Google Chrome and Mozilla Firefox. Most affect browsers installed on Windows Operating Systems. Changes made by browser hijackers may seem insignificant, however, it is impossible to undo them as long PUAs are installed. They prevent users from reverting the settings and change them back when attempts are made.
Another downside of having unwanted apps of this type installed is that they usually gather browsing-related (and other) data. Browser hijackers collect IP (Internet Protocol) addresses, geo-locations, search queries, URLs of visited websites, pages viewed, and so on. PUAs might also record sensitive/personal information. Developers use the data to generate revenue by sharing or selling it to third parties (potentially, cyber criminals). These people misuse private data to generate revenue. Thus, having data tracking apps such as browser hijackers installed might cause problems relating to privacy, browsing safety, and identity theft. You are advised to remove all PUAs immediately.
| Name | Safari redirect malware |
| Threat Type | Mac malware, Mac virus |
| Symptoms | Your Mac became slower than normal, you see unwanted pop-up ads, you get redirected to shady websites. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), fake flash player installers, torrent file downloads. |
| Damage | Internet browsing tracking (potential privacy issues), displaying of unwanted ads, redirects to shady websites, loss of private information. |
| Malware Removal (Mac) | To eliminate possible malware infections, scan your Mac with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
Most PUAs of this type (browser hijackers) are virtually identical: developers promote them by promising 'useful' features and tools, however, these are merely attempts to trick people into downloading/installing them. Once installed, they provide none of the functionality promised. On the contrary, they cause unwanted redirects, change browser settings, and gather data. They are designed only to generate revenue for their developers. Some examples of browser hijackers that target Safari include homesweeklies.com, weknow.ac, and playsearchnow.com.
How did Safari Redirect Virus install on my computer?
In some cases, PUAs can be downloaded from their (supposedly official) websites, however, users often download/install them unintentionally through intrusive ads that, once clicked, execute scripts designed to download and install PUAs, or when software developers use a deceptive marketing method called 'bundling'. Bundling is used to trick people to install potentially unwanted apps together with other, regular software. Developers hide bundled apps in 'Custom', 'Advanced' (and other similar settings) of the installation (or download) set-ups. Most users cause inadvertent installations (or downloads) by skipping installation/download procedures without checking available settings and leaving them unchanged. In other cases, they cause infiltration by clicking untrustworthy, deceptive advertisements.
How to avoid installation of potentially unwanted applications?
Download software from official sources and using direct links only. Avoid using third party software downloaders (and installers), since these are usually monetized by promoting potentially unwanted apps. Avoid using peer-to-peer networks (such as torrent clients, eMule, and so on) or various unofficial, dubious websites. Install software with care - do not skip installation or download steps and analyze each step by checking all available settings/options such as 'Custom', 'Advanced', and other similar parts. Bear in mind that most malicious (or other untrustworthy) advertisements often seem legitimate, however, by clicking them, many users are redirected to adult dating, gambling, pornography, or other untrustworthy websites. If you experience unwanted redirects, it is possible that PUAs are installed on the browser or computer. Check the list of installed apps, such as extensions, add-ons, and plug-ins on the browser and remove all suspicious, unwanted entries immediately. Also apply this to programs installed on your computer. If your computer is already infected with browser hijackers, we recommend running a scan with Combo Cleaner Antivirus for macOS to automatically eliminate them.
Instant automatic Mac malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of Mac malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner for MacBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Quick menu:
- STEP 1. Remove browser hijacker related files and folders from OSX.
- STEP 2. Remove unwanted browser redirects from Safari.
- STEP 3. Remove browser hijackers from Google Chrome.
- STEP 4. Remove rogue extensions from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Safari Redirect Virus redirect removal:
Remove Safari Redirect Virus related potentially unwanted applications from your 'Applications' folder:
Click the Finder icon. In the Finder window, select 'Applications'. In the applications folder, look for 'MPlayerX','NicePlayer', or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Remove safari redirect malware related files and folders:
Click the Finder icon, from the menu bar, choose Go, and click Go to Folder..
Check for adware-generated files in the /Library/LaunchAgents folder:
Safari Adware Virus Protection
In the Go to Folder.. bar, type: /Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware-generated files in the /Library/Application Support folder:
In the Go to Folder.. bar, type: /Library/Application Support
In the 'Application Support' folder, look for any recently-added suspicious folders. For example, 'MplayerX' or 'NicePlayer', and move these folders to the Trash.
Check for adware-generated files in the ~/Library/LaunchAgents folder:
In the Go to Folder bar, type: ~/Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware-generated files in the /Library/LaunchDaemons folder:
In the Go to Folder.. bar, type: /Library/LaunchDaemons
In the 'LaunchDaemons' folder, look for recently-added suspicious files. For example, 'com.aoudad.net-preferences.plist', 'com.myppes.net-preferences.plist', 'com.kuklorest.net-preferences.plist', 'com.avickUpd.plist', etc., and move them to the Trash.
Scan your Mac with Combo Cleaner:
If you have followed all the steps in the correct order you Mac should be clean of infections. To be sure your system is not infected run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file double click combocleaner.dmg installer, in the opened window drag and drop Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates it's virus definition database and click 'Start Combo Scan' button.
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays 'no threats found' - this means that you can continue with the removal guide, otherwise it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Safari redirect malware homepage and default Internet search engine removal from Internet browsers:
Remove malicious extensions from Safari:
Remove safari redirect malware related Safari extensions:
Open Safari browser. From the menu bar, select 'Safari' and click 'Preferences..'.
In the preferences window, select 'Extensions' and look for any recently-installed suspicious extensions. When located, click the 'Uninstall' button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for normal browser operation.
My Safari Has A Virus
Change your homepage:
In the 'Preferences' window, select the 'General' tab. To set your homepage, type the preferred website URL (for example: www.google.com) in the Homepage field. You can also click the 'Set to Current Page' button if you wish to set your homepage to the website you are currently visiting.
Change your default search engine:
In the 'Preferences' window, select the 'Search' tab. Here you will find a drop-down menu labelled 'Search engine:' Simply select your preferred search engine from the drop-down list.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
Remove malicious plug-ins from Mozilla Firefox:
Remove safari redirect malware related Mozilla Firefox add-ons:
Open your Mozilla Firefox browser. At the top right corner of the screen, click the 'Open Menu' (three horizontal lines) button. From the opened menu, choose 'Add-ons'.
Choose the 'Extensions' tab and look for any recently-installed suspicious add-ons. When located, click the 'Remove' button next to it/them. Note that you can safely uninstall all extensions from your Mozilla Firefox browser - none are crucial for normal browser operation.
Change your homepage:
To change your homepage, click the 'Open Menu' (three horizontal lines) button and choose 'Preferences' from the drop-down menu. To set your homepage, type the preferred website URL (for example: www.google.com) in the Homepage Page.
Change default search engine:
In the URL address bar, type 'about:config' and click the 'I'll be careful, I promise!' button.
In the 'Search:' field, type the name of the browser hijacker. Right click on each of the found preferences and click 'Reset' from the drop-down menu.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Remove malicious extensions from Google Chrome:
Remove safari redirect malware related Google Chrome add-ons:
Open Google Chrome and click the 'Chrome menu' (three horizontal lines) button located in the top-right corner of the browser window. From the drop-down menu, choose 'More Tools' and select 'Extensions'.
In the 'Extensions' window, look for any recently-installed suspicious add-ons. When located, click the 'Trash' button next to it/them. Note that you can safely uninstall all extensions from your Google Chrome browser - none are crucial for normal browser operation.
Change your homepage:
Click the 'Chrome menu' (three horizontal lines) button and choose 'Settings'. In the 'On Startup' section, click the 'Set pages' link near to the 'Open a specific page or set of pages' option. Remove the URL of the browser hijacker (for example trovi.com) and enter your preferred URL (for example, google.com).
Safari Virus Removal
Change default search engine:
Safari Adware Virus
Click the 'Chrome menu' (three horizontal lines) button and choose 'Settings'. In the 'Search' section, click the 'Manage search engines..' button. In the opened window, remove the unwanted Internet search engine by clicking the 'X' button next to it. Select your preferred Internet search engine from the list and click the 'Make default' button next to it.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.

